NIS-2 in Germany: opportunities, risks and strategic decisions
Why NIS-2 is crucial now
The European NIS 2 Directive marks a milestone for cyber security in the EU. It aims to create a uniform level of protection, make critical infrastructures more resilient and reduce dependence on non-European IT providers.
Germany now faces the challenge of transposing these requirements into national law. However, the current debate shows that there is a dangerous gap between aspiration and reality.
Political background and objectives
The NIS 2 Directive is part of a European security strategy. It pursues three core objectives:
- Harmonization of the internal market through uniform minimum standards,
- Strengthening the cyber resilience of critical facilities,
- Transparent supervision and enforcement via state authorities.
However, Germany risks missing these targets with the current draft law. According to the Economic Council of the CDU, the government is downgrading minimum standards to an upper limit and withdrawing from central responsibilities.
Criticism of the German draft law
IT baseline protection for ministries only
Only federal ministries are required to implement BSI IT baseline protection. Downstream authorities - many of which are KRITIS-relevant - remain exempt. This creates serious security gaps.
Dynamic references instead of fixed standards
Instead of clear legal requirements, the draft dynamically refers to "current versions" of BSI standards. This harbors the risk that security levels can be lowered without parliamentary oversight.
Minimum standards as a goal instead of a basis
Minimum requirements may only form the lower limit. However, the draft considers them to be sufficient - a risky strategy in times of hybrid threats.
National certification obligation
The proposed blanket authorization for national certifications could fragment the European internal market and weaken the competitive position of German providers.

Strategic perspectives from politics and business
On September 10, 2025, the Federal Cyber Security Commission discussed the realignment of German digital policy at the Academy of the Konrad Adenauer Foundation (Berlin).
BMDS (Federal Ministry for Digital and State Modernization) wants to create a sovereign, Europe-wide connectable infrastructure with the "Germany Stack".
Henri Schmidt MdB (CDU/CSU) called for a binding quota for European IT solutions and warned of security policy risks due to dependencies.
Andreas Reisen (BMI) presented the implementation of the NIS-2 directive and announced the "Cyber Dome" program as a partially automated protective shield.
The discussion made it clear that Germany needs a clear, long-term strategy - with specific targets for the next three to five years.
NIS-2 at a glance: Figures and obligations
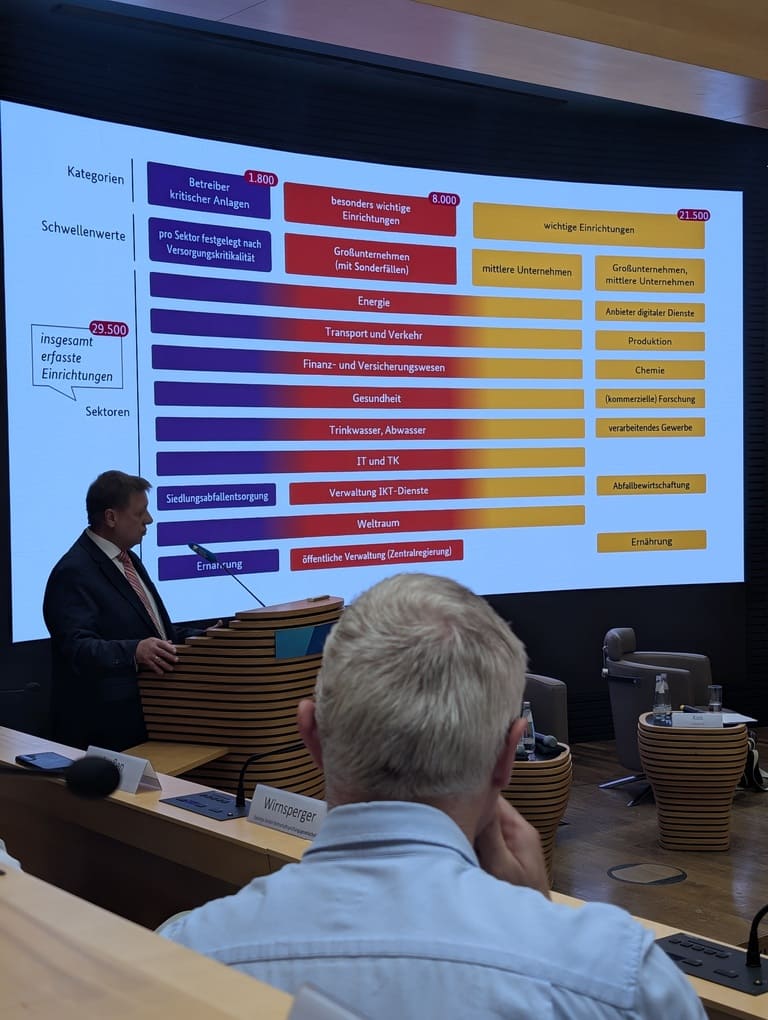
Facilities affected: around 29,500 (including 8,000 particularly important and 21,500 important facilities).
Sectors: energy, transportation, finance, health, research, chemicals, production, food, water/wastewater, IT/telecommunications, administration, space and many more.
Duties:
Registration and risk management,
Incident reporting obligation,
Obligation to provide evidence every 3 years (for particularly important facilities),
Use of systems for attack detection.
Supervision is carried out by the BSI (Federal Office for Information Security) - partly ex-ante, partly ex-post, depending on the criticality of the facility.
Recommendations for authorities and companies
Make IT baseline protection mandatory - for all authorities, not just ministries.
Firmly anchor safety standards in the law - no dynamic references.
Exceed minimum standards - higher requirements must apply to critical systems.
Use the C5 criteria catalog - as a binding procurement standard for cloud solutions.
Create transparency - regular, publicly accessible reports on the status of information security.
Germany at the crossroads of security policy
The implementation of the NIS 2 Directive is more than just a technical issue. It determines digital sovereignty, economic competitiveness and national security.
Germany must not be the weakest link in its own security architecture. Instead, it needs a coherent, consistent and legally binding strategy - with the state as the beacon of cyber security.





